EVENTS CALENDAR
UPCOMING EVENTS



ISSA Kentuckiana - 2026 March
REGISTER ON EVENTBRITE: https://www.eventbrite.com/e/1964504222011?aff=oddtdtcreator





Holiday Dinner 2025
2025 Holiday Dinner - Members only social event.
Location: Captain’s Quarters
Dinner event for Members and a guest
Members will directly receive registration details.




Louisville InfoSec Conference
Louisville Metro InfoSec Conference 2025
More Details:
https://www.louisvilleinfosec.com/
Registration:




Hack Red Con 2025 (Sponsor)
ISSA Kentuckiana is a proud sponsor of Hack Red Con 2025!
As a sponsor we are offering ISSA Kentuckiana members free tickets! Supplies are limited, act now.
Members, check for communications from ISSA Kentuckiana!


Meeting
Topic: An Elegant Test, For a More Civilized Age
Description: Come explore the landscape of offensive cybersecurity testing with Dean Dorton! We will guide you through the different types of testing, from Penetration Testing to Red Teaming, Purple Teaming, and any other color of lightsaber you can think of. Starting with the initial scoping and planning, and following through the final report and beyond, you can see all the factors that contribute to a successful test (or doom it to failure). So, turn off your targeting computers and let us help you navigate this asteroid field of decisions and terminology (“never tell me the odds!”). We will share our hard-earned advice from decades of experience, so that you can have the best chance of success from your next offensive engagement.
Presentation by: Garrett Pieratt & John Askew
Sponsor: : Dean Dorton
Registration: https://www.eventbrite.com/e/issa-kentuckiana-2025-may-tickets-1076540815559?aff=oddtdtcreator
Location
We would like to thank Farm Credit Mid-America for hosting our event!
12501 Lakefront Place Louisville, KY 40299
(Farm Credit Mid-America Building - Schoolhouse East (132); Schoolhouse West (130))
CPE Credits
ISSA Kentuckiana members with Confirmed attendance of this event are eligible for 1 CPE credit
Time
The meeting will be from 11:30 AM - 1:00 PM Eastern. Lunch will be provided.
RSVP required!
Registration is required for building access!
ISSA Kentuckiana members with Confirmed attendance of this event are eligible for 1 CPE credit

Meeting
Topic: Bringing Zero Trust Segmentation Within Reach
Description: Whether they were abandoned or simply ineffective, most CXOs have seen segmentation projects produce underwhelming results. Learn how your organization can move from network-based segmentation to zero trust segmentation for more granular control IT teams can actually execute. This session covers unique features of the zero trust approach to microsegmentation, how to create “a network of one” for OT/IoT devices, and the benefits of implementing east/west segmentation.
Presentation by: Ben Corll, CISO in Residence, Zscaler
Ben is a 25-year veteran in the cybersecurity industry with a passion to protect enterprise organizations. He has spent his career establishing security programs for companies of all types and sizes, from 500 to 50,000. Ben has held just about every technical security role, from AV, firewall, SIEM, and DLP management, to security architect, and CISO roles.
Sponsor: : Zscaler
Registration: https://www.eventbrite.com/e/issa-kentuckiana-2025-june-tickets-1076541176639?aff=oddtdtcreator
Location
We would like to thank Farm Credit Mid-America for hosting our event!
12501 Lakefront Place Louisville, KY 40299
(Farm Credit Mid-America Building - Schoolhouse East (132); Schoolhouse West (130))
CPE Credits
ISSA Kentuckiana members with Confirmed attendance of this event are eligible for 1 CPE credit
Time
The meeting will be from 11:30 AM - 1:00 PM Eastern. Lunch will be provided.
RSVP required!
Registration is required for building access!
ISSA Kentuckiana members with Confirmed attendance of this event are eligible for 1 CPE credit

Social Event sponsored by Guidepoint Security
ISSA Kentuckiana Members Social Event at Five Iron Golf sponsored by Guidepoint Security
We’re gathering local leaders for an evening at Five Iron Golf!
Join GuidePoint, ISSA Kentuckiana, and your peers for a fun afternoon of indoor golf and networking.
Five Iron Golf
Date: Friday, March 14th
Time: 1:30-4:00pm
Location: Five Iron Golf | 836 E Market St, Louisville, KY 40206
Members and Invite only
Registration Required

Meeting
Topic: Strategic Vulnerability Response
Description: Organizations often find themselves struggling to know where to start or improve in vulnerability management, which vulnerabilities to address first, and how to efficiently allocate time and resources. Emphasizing the criticality of a strategic, risk-based approach is paramount in today's landscape, where vulnerability management sometimes is treated like incident response.In this session, we'll explore:
Why reactionary vulnerability management often falls short.
The business benefits of a risk-based VM approach.
The importance of forging cross-departmental alliances from the onset.
Crafting a compelling business case for broader team involvement in vulnerability management initiatives.
Presentation by: Furey DiDomenico, SR Security Architect and Josh List, Principal VM Consultant.
Sponsor: : Guidepoint Security
Registration: https://www.eventbrite.com/e/issa-kentuckiana-2025-march-tickets-1076538157609?aff=oddtdtcreator
Location
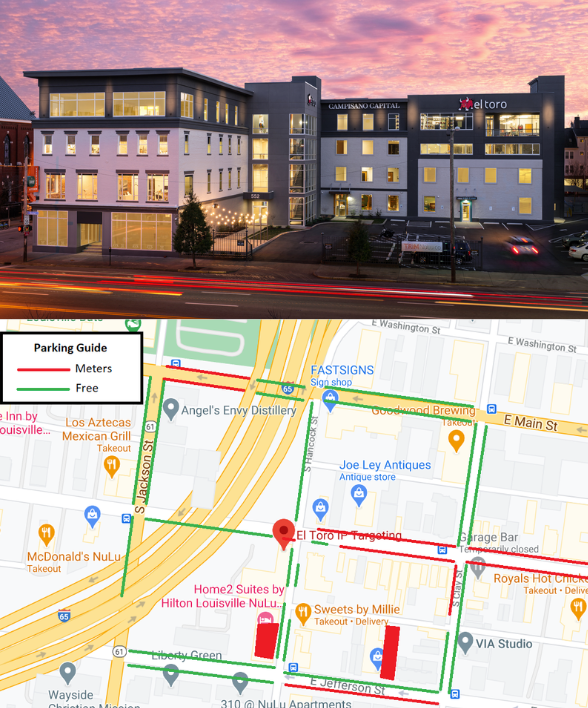
El Toro IP Targeting in Nulu
552 E. Market Street
The meeting will be held on the 2nd floor in the event space.
Parking under the underpass and along Hancock is typically most ideal (free).
Time
The meeting will be from 11:30 AM - 1:00 PM Eastern. Lunch will be provided.
RSVP required!
Registration is required for building access!
ISSA Kentuckiana members with Confirmed attendance of this event are eligible for 1 CPE credit

Secure Digital Conference 2025
ISSA Kentuckiana is sponsoring the Kentuckiana ISACA’s Secure Digital Conference 2025
To encourage our members to attend we will not be having a ISSA meeting in Feb.
Discount codes will be emailed to our members.
Registration info:

Competency Group Meetup - Physical Security (Members and Invited guests only)
Topic: Physical Security - General
We’re excited to announce the very first meetup for our Physical Security Competency Group—actually, our first competency group meetup ever!
Details:
📅 When: 1/31 11:00 AM
📍 Where: Starbucks (Corner of Hurstbourne Pkwy and Shelbyville Rd)
101 N Hurstbourne Pkwy, Louisville, KY 40222
What to Expect:
Our competency group meetups are informal gatherings designed to bring together professionals with shared interests, this meetup will focus on physical security. It’s a great opportunity to network, exchange ideas, and enjoy some casual conversation.
A Few Reminders:
Starbucks requires all patrons to make a purchase to use their space.
Seating/Space will be limited since this is a casual meetup in a public setting.
Erich and I look forward to seeing you there!
Location
Starbucks - Hurstbourne / Shelbyville Rd
101 N Hurstbourne Pkwy, Louisville, KY 40222
This event is for members and invited guests only. If interested inquire with a member OR join our Discord and ask there.

API Security Testing Workshop
The ISSA Kentuckiana Chapter, in partnership with Ellipsis Information Security LLC, is excited to present an immersive, hands-on information security workshop focused on API Security Testing.
This day-long event offers a unique opportunity to learn directly from a globally recognized application security expert, who brings over a decade of experience teaching professionals of all skill levels.

Meeting
Topic: Securing Data in a Connected World: Strategies for Protecting APIs, Detecting Fraud, and Streamlining API Security Testing
Description: APIs provide a universal attack vector for hackers that are commonly overlooked when it comes to security and facilitate complex business processes that regularly fall victim to fraudulent and abusive activities. Learn how APIs can be protected to prevent hackers from stealing sensitive information or taking advantage of business logic to benefit themselves from design flaws.
Presentation by: Patrick Mawyer, Sr Sales Engineer @ Traceable
Sponsor: Traceable
Registration: https://www.eventbrite.com/e/issa-kentuckiana-2025-january-tickets-1057299454129?aff=oddtdtcreator
Location
We would like to thank Farm Credit Mid-America for hosting our event!
12501 Lakefront Place Louisville, KY 40299
(Farm Credit Mid-America Building - Schoolhouse East (132); Schoolhouse West (130))
Time
The meeting will be from 11:30 AM - 1:00 PM Eastern. Lunch will be provided.
RSVP required!
Preregistration is required for building access!
ISSA Kentuckiana members with confirmed attendance of this event are eligible for 1 CPE credit

Holiday Dinner 2024
2024 Holiday Dinner - Members only social event.
Location: Captain’s Quarters
Dinner event for Members and a guest
Members will directly receive registration details.

Meeting
Topic: Securing Derby 150 – Protecting the Legacy of the Kentucky Derby
Description: This presentation will emphasize the roles and collaborations among the Churchill Downs teams with various law enforcement agencies, and the integration of physical security with cybersecurity efforts that it required to protect KY Derby 150.
Presentation by: Jason Payton - Director, Cybersecurity Risk Management | Churchill Downs
Sponsor: Brinqa
Registration: https://www.eventbrite.com/e/issa-kentuckiana-2024-december-tickets-920821250147
Location
We would like to thank Farm Credit Mid-America for hosting our event!
12501 Lakefront Place Louisville, KY 40299
(Farm Credit Mid-America Building - Schoolhouse East (132); Schoolhouse West (130))
Time
The meeting will be from 11:30 AM - 1:00 PM Eastern. Lunch will be provided.
RSVP required!
Preregistration is required for building access!
CPE Credit
ISSA Kentuckiana members with Confirmed attendance of this event are eligible for 1 CPE credit

Meeting
Topic: If These Doors Could Talk
Description: An introduction to lock picking and physical security.
Presentation by: Brad Eadens
Sponsor: Trend Micro
Registration: https://www.eventbrite.com/e/issa-kentuckiana-2024-november-tickets-920818953277
Location
We would like to thank Farm Credit Mid-America for hosting our event!
12501 Lakefront Place Louisville, KY 40299
(Farm Credit Mid-America Building - Schoolhouse East (132); Schoolhouse West (130))
Time
The meeting will be from 11:30 AM - 1:00 PM Eastern. Lunch will be provided.
RSVP required!
Preregistration is required for building access!
CPE Credit
ISSA Kentuckiana members with Confirmed attendance of this event are eligible for 1 CPE credit

Hack Red Con 2024
ISSA Kentuckiana is a sponsor of Hack Red Con 2024!
As a sponsor we are offering the Kentuckiana security community a free code for tickets!
(supply is limited so claim your ticket ASAP!)
HRC_PROMO_METRO
Use the above code at checkout:
https://www.hackredcon.com/event/hack-red-con-2024-1/register